KMS : Public Key Cryptography : Digi-Sign.com
- Cryptomathic Key Management System [KMS]
-
The Cryptomathic Key Management System [KMS] is built around a three-tier architecture with an application server that provides services for a number of client applications; a database server that is used as repository; and a network interface to the Network Service Provider(s) [NSP] that uses a Hardware Security Module [HSM] to secure all keys.
The KMS is used for managing the system keys and to monitor the availability and performance of the NSPs:
- How it Works
-
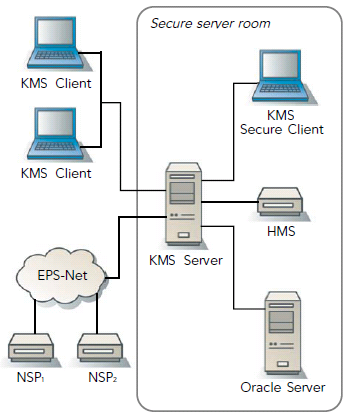
Secure operations have been a design goal from the beginning of the project. The KMS is located on a physically secured operations site to which only a limited number of system operators have access.
Smart cards are used in order to provide strong user authentication. All sensitive operations must be performed within the secured area and with the presence of multiple operators. All non-sensitive operations can be carried out by auditors and operators who are not allowed on the secured operations site.
Choose your KMS >>

